[ad_1]
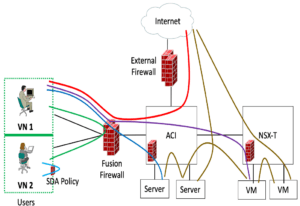
I was examining some SD-Accessibility documentation I’d published and came throughout a diagram I identified practical in discussing protection and the place it is enforced. There’s only a single aspect of it that is distinct to SD-Entry (“SDA”). If I’ve place this into a site right before, apologies, I’m not viewing it.
I connect with this the “Who Enforces What” protection diagram and associated dialogue. It can be extremely practical when trying to comprehend requirements, who owns which areas of stability, etcetera.
Preferably, you deal with all the kinds of stream discussed down below at the very least after. And at most as soon as – duplication of ACL enforcement regulations generally potential customers to wasted effort and hard work and more troubleshooting thanks to enhanced complexity.
Who Enforces What?
Here’s the famous (infamous?) diagram…
Discussion: Person Site visitors
Let’s dispose of the still left SDA component immediately.
If you have SDA in your campus network(s), you can use SDA coverage to have distributed enforcement of policy amongst distinct user/machine SGTs (Safety Team Tags). If you really don’t have SDA, then some thing else desires to do that, possibly VRF-Lite and/or VLANs to a firewall. This type of flow is indicated by the pale blue arc in the higher than diagram.
The VNs are just VRFs (for non-SDA men and women, anyway). I feel of VRFs as heavier isolation mechanisms. They are heavier because a lot more configuration hard work is required to deploy them, but also mainly because they deliver more robust boundaries in between various user or machine groups, logically different networks for differing safety demands.
Frequently, 1 operates VRFs (or VLANs) above to a fusion firewall (FFW) pair to management what targeted visitors is allowed between VNs which might contain end users, PCI website traffic, IOT machine visitors, and many others.
This type of move is indicated by the eco-friendly arc in the earlier mentioned diagram.
Flavors of Enforcement
So, the earlier mentioned covered the subsequent sorts of flows:
- Person to consumer (very same SGT) – almost never any enforcement
- User to user (different SGT)
- VN/VRF to unique VN/VRF
The different remaining and colored strains in the previously mentioned diagram indicate website traffic flows you might want security procedures used to. The flows in problem are:
- Consumer to bodily server
- User to VM
- Actual physical server to bodily server
- Bodily server to VM
- VM to VM
- Person to World wide web
- Server to Net
- VM to Net
Discussion: Internet Sure Flows
Let us take a closer glance at the flows just detailed. We’ll deal with the checklist from the bottom up, kind of by the approach of elimination.
The flows to the World-wide-web, the last three earlier mentioned, are probably uncomplicated: that is why you have an World wide web firewall. Completed! (And possibly some anti-malware and so forth., measures thrown in as well, but which is a broader scope than I want to tackle here.)
Dialogue: VM and Server Sure Flows
That is, it flows to a VM or a server.
If you are operating VMware NSX, you are almost absolutely (in my practical experience) utilizing its security, or a firewall alternative integrated with NSX to management who or what can get to each and every VM or team of VMs. Accomplished.
If you are nevertheless carrying out ESXi, then ACI might be delivering controls on what will get to VMs and servers.
No ACI? Then you could not be filtering what receives to servers and VMs. Or you have a firewall in some way situated “in front of” the VMs and servers, just for that purpose.
Discussion: Consumer Flows
And which is where by the FFW commences getting somewhat helpful. It is in a very good position to (A) intercept user to server or VM flows, and (B) do so based mostly on characteristics like ISE or Home windows teams or SGTs.
That can be useful in one more way. Possibly you then have ACI or NSX or a firewall intercepting server-bound traffic. Then it’s possible you really do not want to have intricate *person* to server policies there, just allow assertion(s) for person source addresses. Separation of operation and workload?
SGTs have constraints. Which is a additional state-of-the-art topic, which I might talk about in a foreseeable future site.
Discussion: But These Physical Servers?
If none of the above fairly function for the physical servers, perfectly, you can generally set just them driving a firewall. Or may have carried out so in the earlier as you migrate most workloads to VMs.
New Types of Enforcement / Zero Have faith in
With agent-centered Zero Believe in or other enforcement mechanisms, you efficiently can set the enforcement of ACLs (or other safety) in the servers and VMs, except for possibly antiques and mainframes. And very similar products and solutions, often from the exact same corporations, for close end users.
For me, Illumio kicked off this established of products, albeit maybe ahead of Zero Trust became as incredibly hot a expression. And now a lot of stability distributors have agent-based mostly protection solutions with centralized controllers.
There is one big rationale I see for the reputation of these types of alternatives. And that is throughput compared to value. Firewalls with N high speed ports have normally been highly-priced, generally some multiplier in the 4 to 10 variety of the cost of a comparably rapid change. The issue is that firewalls centralize and mixture all the targeted visitors.
By way of contrast, agent-based mostly options distribute the workload. They do, in effect, bring about a overall performance tax on the VM or server aspect. Whilst some the latest tech blogs look to advise that impact can be tremendously lowered for some operating methods (Linux, BPF?).
An additional big benefit of agent-centered mechanisms is digital segmentation: isolating teams of customers or equipment (or a blend of the two) without the need of community plumbing in the type of VLANs, VRFs, and equivalent added complexity. Trades unit-based “plumbing” for virtual isolation, preserving the network device component less complicated.
I’ll now swiftly adjust the subject matter, as I’m not monitoring that distinct region at all intently.
Summary
I remarkably suggest that everybody in IT realize where just about every variety of safety ACL/filtering is staying carried out and who is accountable for that piece of general safety. The diagram over is just one software for talking about this and overall community stability style and design. And if you really do not like it, it’s uncomplicated plenty of to come up with a little something extra suited for your community or the way your brain functions.
Backlinks
https://netcraftsmen.com/securing-sd-obtain-site visitors/
https://netcraftsmen.com/sd-obtain-and-the-internet-of-issues-iot/
https://netcraftsmen.com/wherever-to-adhere-the-firewall-element-1/
https://netcraftsmen.com/where by-to-stick-the-firewall-component-2/
https://netcraftsmen.com/web-edge-alternate-stability-remedies/
[ad_2]
Supply connection